Keeping track of different passwords for various accounts becomes tricky, fast. Remembering them all is not easy, and jotting them down on random pieces of paper just makes them easier to lose. A solution that's both organized and secure would help immensely in managing this mess.
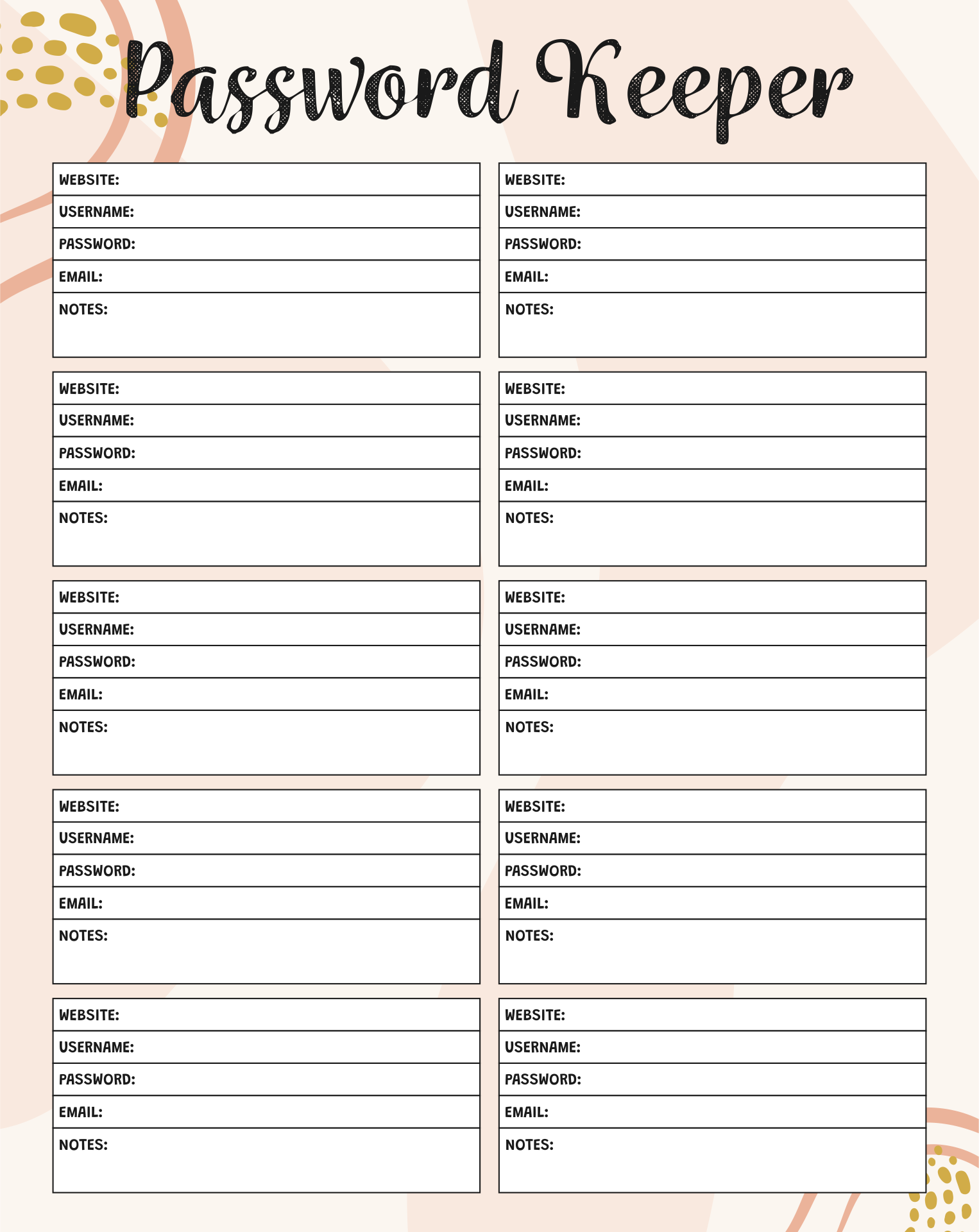
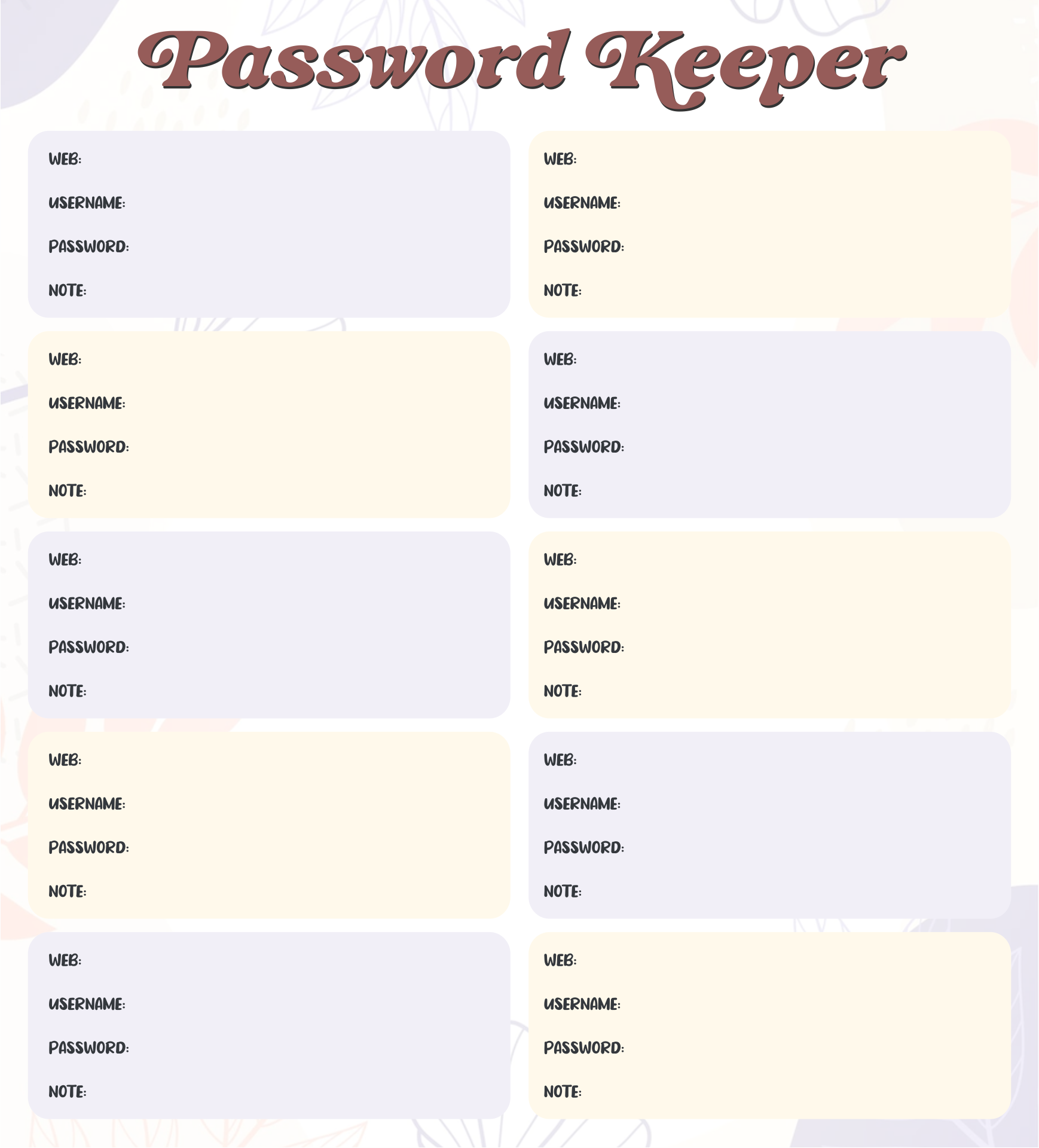
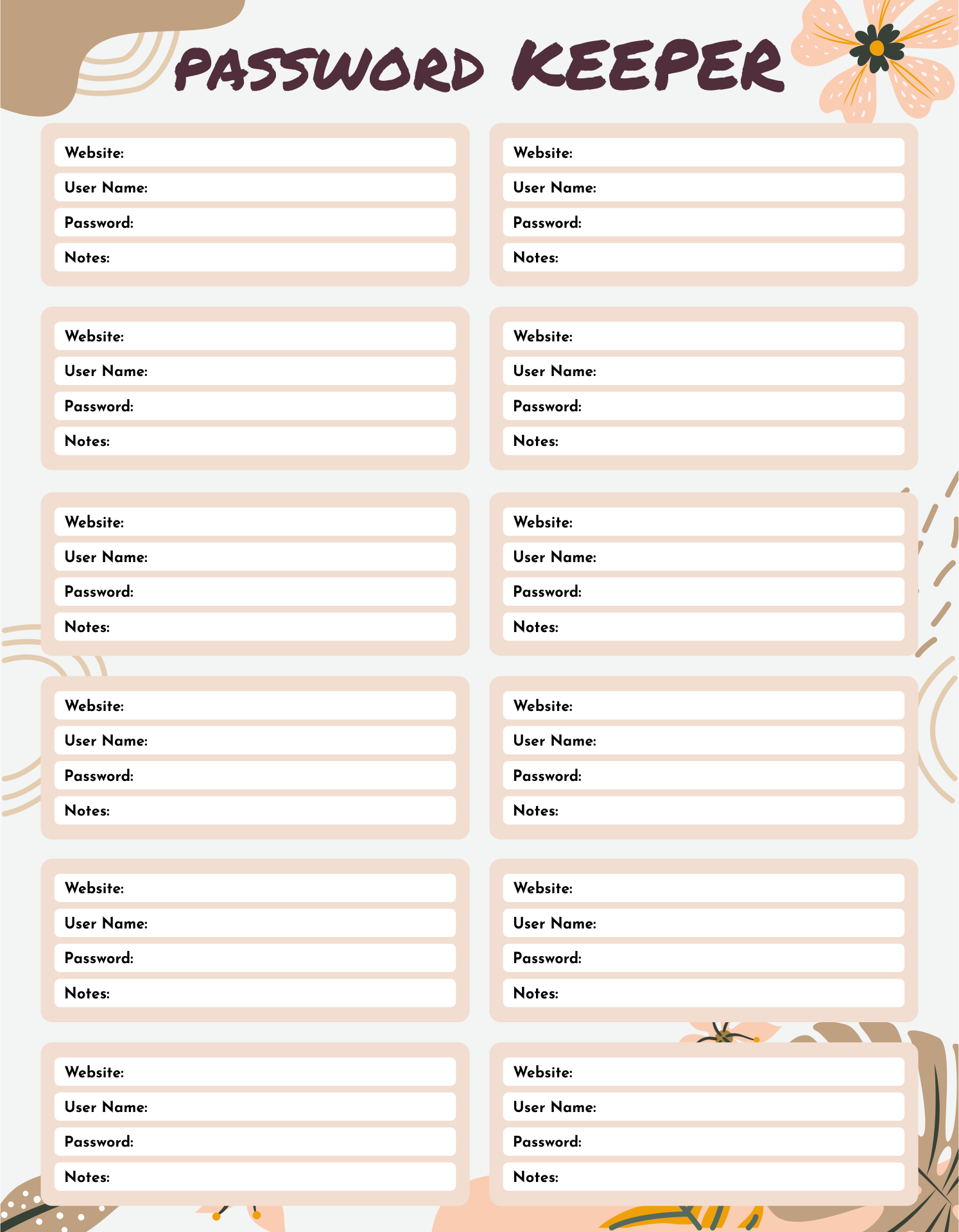
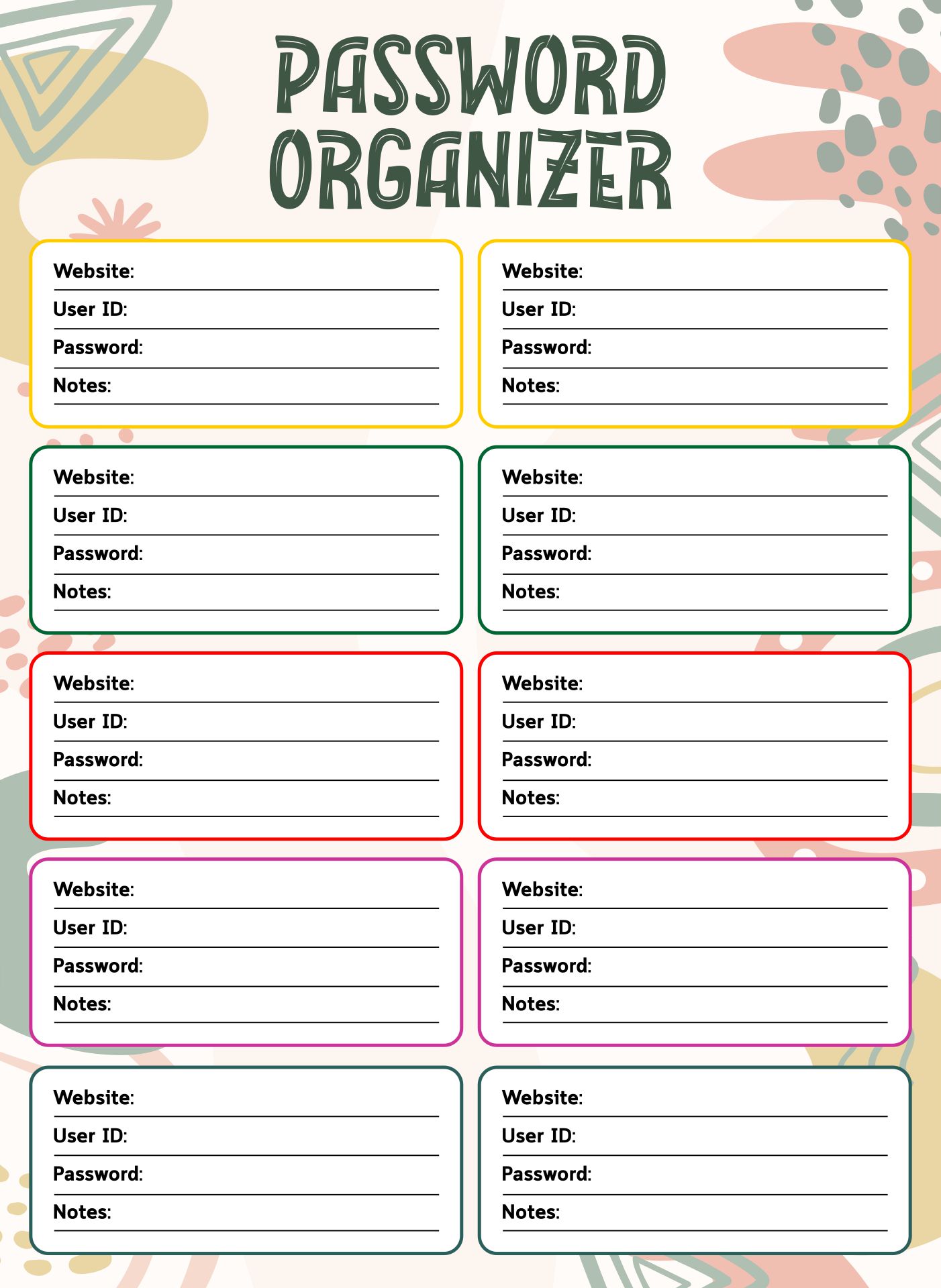
We created a printable for keeping all those tricky passwords in one place. Small enough to tuck away, but organized so you won't be flipping pages to find your info. Sections are laid out for website, username, and password, making updates easy peasy. Keeps things straightforward and secure, no more resetting passwords every other week.

Because they are used to safeguard digital assets and thwart illegal access, passwords are a crucial component of cybersecurity. Personal accounts, business networks, and governmental systems all employ password security. Strong passwords are advised by cybersecurity professionals as part of a comprehensive cybersecurity plan. It's also important to safely clean your computer from system junk, so you can check free Mac cleaners, for example.
Passwords serve as the initial layer of security against cyberattacks. Passwords are used to safeguard sensitive data and to prevent unwanted access to digital assets. To get access to credentials and breach networks, cybercriminals might employ a variety of approaches such as phishing, social engineering, or brute-force assaults. Strong passwords can aid in the prevention of these assaults and provide protection against cyber dangers.
It is risky to use the same password across several websites since it compromises your identification and online security. For each account, choose a unique, safe password, and use a password manager to help you remember them. By doing this, you can protect your personal information, prevent unauthorized access, and maintain control over your online security.
Although they are crucial for protection, strong passwords may be difficult to remember. Too long or complicated passwords can be hard to remember, which leads many users to write them down or use the same password across several accounts, both of which weaken security. Following are some typical difficulties with hard passwords that may be overcome:
Have something to tell us?
Recent Comments
The Password Book Printable is a handy and practical resource for keeping track of my passwords in an organized and efficient way. It has made managing my online accounts a breeze! Thank you for creating such a useful tool.
This Password Book Printable is such a practical and organized way to keep track of my passwords! Love how this resource makes it easy to stay on top of my online security.
This Password Book Printable is such a handy tool! It keeps all my passwords organized and easily accessible. Thanks for simplifying my digital life!